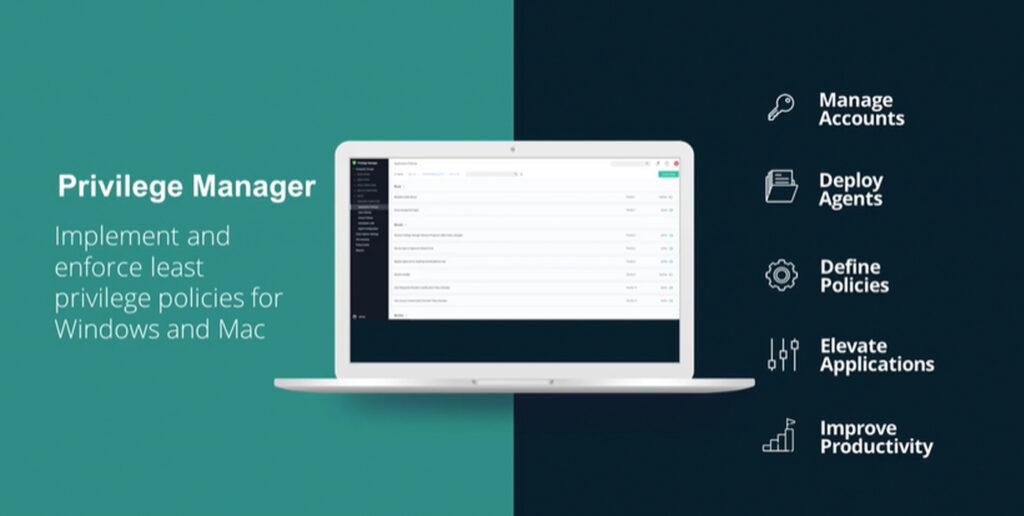
Apple operating system increasingly the target of malware
MacOS has the reputation of being a relatively attack-proof operating system. Not only among Apple users, MacOS has always been far less susceptible to malware and cyberattacks than the market leader Windows. The fact is, however, that even Mac users are not immune to compromises or dangerous infections, as there is more and more malware […]
Apple operating system increasingly the target of malware Read More »