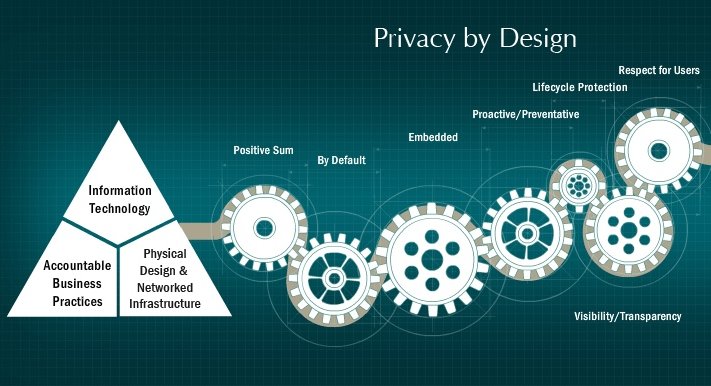
The 7 foundational principles of privacy by design
Dr. Ann Cavoukian, Information and Privacy Commissioner of Ontario, Canada, provides extremely informative insights on Privacy by Design on her website. The objectives of Privacy by Design — ensuring privacy and gaining personal control over one’s information and, for organizations, gaining a sustainable competitive advantage, she states, may be accomplished by practicing the following seven foundational […]
The 7 foundational principles of privacy by design Read More »