Announcements & appointments
Recognised marketer, Hélène Blanchette, senior manager of Innovation & Business Transformation, Fuji Xerox Asia Pacific…
Mobile Marketing Academy brings intensive mobile training to Asia-Pacific marketers
As the Asia Pacific region is expected to fuel the growth of mobile marketing in…
Moontoast’s ultimate industry guide to social rich media advertising
Social advertising will continue its strong momentum as innovations in the field are poised to…
Exclusive interview: cybercrime and security measures from an Asian perspective
Asian eMarketing had the opportunity to interview Wahab Yusoff, Vice President of McAfee South Asia,…
Privacy is a 2-way road
Privacy is the right to be left alone, or how would you describe it in…
Increasing android malware points out cybercrime’s intricacy
According to eMarketer’s latest forecast, mobile is making inroads in digital ad spending throughout the…
Gartner: big data, gamification and 3D printing hype reached its peak
Gartner published just recently its new outlook “Hype Cycle for Emerging Technologies”, in which it…
Novell‘s protection suite provides security management, disk encryption and patch management for endpoints
BYOD, mobility, multiple screens, the cloud, file-sharing … the endless possibilities of cyberspace in today’s…
Trustwave and TNS join forces to protect payment card data with POS encryption service
Last week Trustwave and Transaction Network Services, Inc. (TNS) announced that they joined forces to…
VMware unveils next-generation network virtualization platform with built-in security model
VMware launched this week a range of new products, one of which is VMware NSX™,…
Lumension Endpoint Security outperforms traditional antivirus according to industry test
In a recent test by the Tolly Group, an independent evaluation and certification provider for…
Steps towards a culture of security
The Internet is an unsafe medium and actually a dangerous place. Due to the euphoria…
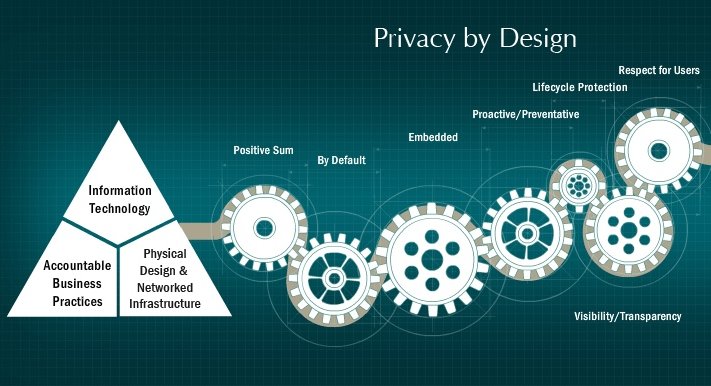
Privacy by default considered by a number of data protection authorities
“Privacy by Default” is a software design concept that intends to prohibit the collection, display,…
The 7 foundational principles of privacy by design
Dr. Ann Cavoukian, Information and Privacy Commissioner of Ontario, Canada, provides extremely informative insights on…
The pros and cons of anonymity: how to make social media integration privacy compliant
Discussions on privacy or surveillance on the Internet are hotly debated these days, often thumping…
Prolexic publishes media guide to counter DDoS cyberthreats
Prolexic just released its brand new “Distributed Denial of Service (DDoS) Media Guide”, we‘d like…
McAfee report warns of sms-stealing banking malware and data-stealing apps
Each quarter, the McAfee Lab team, consisting of 500 multidisciplinary researchers from 30 countries, is…
Data privacy trends in Asia Pacific‘s highly fragmented legislative environment
Forrester‘s senior analyst, Masami Kashiwagi, has been researching data privacy laws in Asia Pacific (AP)…
Your 8 step defense strategy to protect your system against targeted attacks
According to Trustwave‘s 22 page eBook „Inside a Hacker‘s Playbook: 10 Targeted Techniques that will…
Secure exchange of data is the cornerstone of the Shareconomy
“Shareconomy” describes the sharing and collective use of information that can lead to increased transparency…
Hotspot security?! Don‘t give cybercriminals the hotspot opportunity!
Mobile surfing has become cheaper, since data roaming prices have fallen. However, if you want…
If cybercriminals have a business model, CISOs need one too!
According to Forrester’s 2012 report „Determine The Business Value of an Effective Security Program –…
Beware of free gifts and tricks to steal your Facebook data
There is no doubt that online spying and hacking are becoming a bigger problem each…
Security maintenance measures to protect your website against malicious cybercrime attacks
Ordering a bikini or summer dress last minute online, or booking a hotel room quickly,…
Aspects of IT security
IT security is a necessary precondition for the operational use of information systems and informational…
XKeyscore revelations show that “nearly everything a user does on the internet” could be under surveillance around the globe
As Glenn Greenwald, journalist at The Guardian, correctly predicted, further NSA unveilings now by far…
Trend Micro warning: avoid the lure of fake movie-streaming sites
In its analysis of data collected from late April to the end of June, Trend…
What Singaporean businesses should know about the PDPA and DNC
In today’s fast-paced information age, massive amounts of personal data are collected, used and even…
Cyber-Ark global advanced threat landscape survey on sophisticated, targeted attacks and what to do about it
Cyber-Ark’s 2013 Global Advanced Threat Landscape survey was published in June this year and reflects…
Announcements & appointments
Omnicom Media Group (OMG) Asia Pacific has promoted Jonathan Mackenzie – former Director of Digital…
APPIES 2013 will award the APPIES Gold to just five of the best
APPIES 2013 will host 35 of Asia’s marketing luminaries who will assess integrated marketing campaigns,…
CMO Council contributes to development of future Asia-Pacific marketing leadership
The Chief Marketing Officer (CMO) Council’s Asia-Pacific branch has partnered with the Singapore Management University’s…
Bringing internet culture and the protection of privacy in line
Concerns about the safety of new services on the Internet are as much part of…
McAfee teaches online safety for kids to over 15,000 children in South East Asia
McAfee announced today that it has reached more than 100,000 youth, parents and teachers around…
Hotspot Shield flourishes since internet users do not feel safe anymore
The electronic wiretapping of user data by intelligence agencies such as the NSA has fundamentally…
Security for the post-PC era: Google Glass requires new perspectives due to altered risks for networked devices
More and more people and devices are connected with each other these days and, thanks…
BYOD puts data at risk – 60 % of companies are vulnerable, survey revealed
A brand new survey from Acronis and the Ponemon Institute reveals that a majority of…
Beware of royal baby spam!
Last month, all media channels reported on Kate and William waiting for the arrival of…
How to keep critical data safe in a world of BYOD
The 15-page “BYOD Survival Guide”, published by Acronis this year, provides five tips for data…
Five fundamentals of modern data protection
According to Veeam’s ten page whitepaper “Five Fundamentals of Modern Data Protection” the protection of…
IPG Mediabrands identifies four native mobile experiences as building blocks for more successful mobile advertising strategies
Initiative, a global communications network within IPG Mediabrands just released the findings of its Mobile…
There is plenty of mobile opportunity out there, but Asian and European consumers have different preferences
Adobe‘s new State of Mobile Benchmark shows that while UK consumers prefer browsing the mobile…
Irdeto’s piracy continuum: understanding the true nature of the piracy problem
According to Irdeto piracy is not a single behavior, but rather a continuum of behaviors…
Actix delivers call trace geo-location for 20 million mobile subscribers in Asia
Actix, an award winning pioneer of software that enables mobile operators to run more effective…
Augmented reality glasses or Google Glass
Augmented Reality Glasses or Google Glass is a wearable computer with an optical head-mounted display…
Connected in the remotest corner of the globe: new InReach SE satellite communicator launched just in time for the holidays in SEA
Delorme’s satellite communicator, the lowest cost bidirectional communication and tracking device in the market, has…
Growth for Opera Mini in Asia
Opera, the Norwegian software company, seems to take off in Asia Pacific, considering the company’s…
State of the app after five years of AppStore – Google Play seems to be catching up
In the first quarter of 2013, nearly 13 billion apps have been downloaded, not to…