Optimize templates for smartphones and don’t allow Outlook to thwart newsletters
Optimizing emails for smartphones is challenging, since they have up-to-the-minute requirements and the fact that…
Unengaged, unmotivated, uninspired: Do these three words describe your workforce?
Research suggests that 87 percent of America’s workforce fails to reach its full potential. Why?…
Hazard source “Mobile Banking”
Security issues are on everybody’s mind and top priority for any business industry, especially for…
Nearly half of Indonesia’s smartphone users not satisfied with their default browsers
Opera conducted a survey in the six biggest cities in Indonesia (Jakarta, Surabaya, Bandung, Yogyakarta,…
Experiencing the future of search with Google Lens and its AI-powered computer vision
At Google’s annual developer conference ‘Google I/O’ 2017, the reactions to the announcement that Google…
Appointments & Announcements
SpeedcastToni Lee Rudnicki International Limited announced that satellite industry veteran Toni Lee…
Cyber-attacks can hit anyone, anytime – you can be next!
As is well-known, online shops require a particularly large number of protection mechanisms to fight…
Ambivalence: Who is responsible for data protection?
The attitude of customers towards data protection remains ambivalent in the digital world, since they…
Advertising on Facebook: What’s allowed and what’s not
Many consumers are critical of Facebook as they fear for the security of their data….
Protect yourself: Recent WannaCryptor ransomware worm puts a spotlight on cybersecurity
Though a worldwide problem, far too many citizens, businesses and governments are still making the…
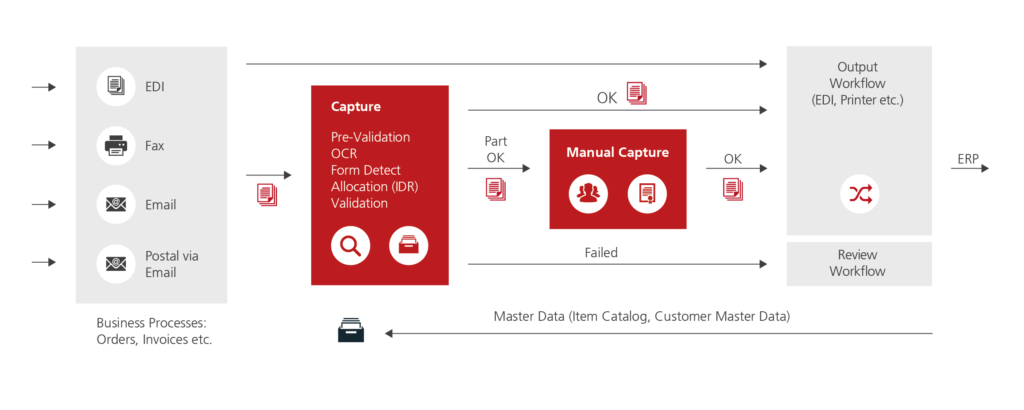
New Retarus ‘Managed Capture Services’ facilitate smooth data interchange and reduced costs and efforts due to ‘Intelligent Document Recognition’
Manually capturing data is not only time and cost intensive, but also prone to error,…
Naiveté, inadvertency and laziness provide perfect breeding ground for ransomware, like WannaCry
More and more networked devices, professionalized hacking groups, and the development of sophisticated malware become…
Asia Pacific’s financial services industry has still a long way to go regarding IT security
IDC highlights in one of its recent reports that IT security of financial services organizations…
Sophisticated technology tracks the culprit to identify violent crime
Violence, extremism and child abuse: A lot of criminal activities are captured in images and…
Hitachi Content Platform ‘Anywhere’ provides for a protected digital workplace
The latest version of Hitachi Content Platform (HCP) Anywhere puts the right tools in the…
Akamai’s Q1 2017 State of the Internet / Security Report
Akamai Technologies, Inc. just released its First Quarter, 2017 State of the Internet / Security…
Security standards for open source CMS
Many companies decide against proprietary licensing models and are increasingly using open-source solutions. They rely…
New partnership provides secure open API offerings for banks and PSPs
Irdeto, the world leader in digital platform security, and Rogue Wave Software, maker of Akana…
Microsoft’s vision for more intelligence — from the cloud to the edge
“In a world of near infinite computing power and an exponential growth in data, we…
Global cybercrime attacks rise 35% in the past quarter with cybercriminals targeting the complex cross-border environment in China
Latest data from ThreatMetrix reveals highly elevated attack levels in China during the past quarter….
Rethink privacy, as the new GDPR takes the upper hand
It’s all haywire when looking at data protection in Europe and I am wondering about…
Retarus issues warning about spam wave claiming to offer stock market tips
The security experts at Retarus are warning users about a spam wave spreading quickly across…
Know the difference between 1st, 2nd, or 3rd party data?
There are different data types, with different meanings, that must be handled differently in today’s…
Appointments & Announcements
Susan Josi and Sangeeta BardeHavas Group is expanding its capabilities and footprint…
Marketing Automation is designed to turn around the increasing trend of underperforming advertising
Advertising is no longer well received by recipients if not delivered exactly when appreciated the…
Advanced marketing automation techniques are still underutilized
Companies rely on marketing attribution to determine which marketing channels have contributed directly or indirectly…
Declining trust in the Internet hinders further development of the digital economy
A new global survey reveals that Internet users are increasingly concerned about their online privacy,…
Move away from seeing things as they have traditionally always been, not to miss the opportunity to truly ‘see’
Where would we be today without WiFi? No more hotspots. No cool internet cafés. Our…
Accelerated Mobile Pages (AMP) meets the need for speed on mobile
Since half of organic traffic comes from mobile devices, you should care about Accelerated Mobile…
An all-encompassing attribution model is still utopian
In general, companies use marketing attribution software to determine how their marketing activities and campaigns…
Identify the full potential of marketing automation by getting rid of wrong perceptions
For quite some time we are accustomed to the fact that, when browsing the Internet,…
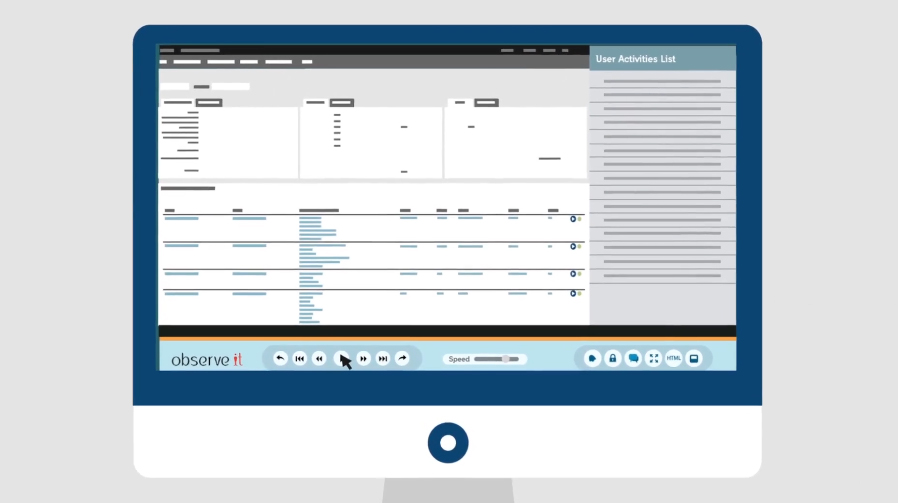
ObserveIT 7.0 speeds up insider threat detection with actionable analytics
ObserveIT, a threat monitoring and analytics solution provider, unveiled new actionable analytics and the ability…
Hotmob launched ALCANZAR, a safety-first demand side platform
Hotmob just announced the launch of its safety-first demand side platform (DSP), ALCANZAR, that focuses…
Legal impact of data protection and management in the digital age
With increasing access to mobile devices and the internet, the amount of data created annually…
Nothing can replace human interaction in marketing – not even automation
Automated marketing is the dream of many companies, as comprehensive data analysis manages to identify…
Ascend2’s ‘State of Marketing Automation’ Report
Ascend2 just published its survey report “State of Marketing Automation”, which the company conducted in…
There’s still more to ‘courting’ clients than ‘swiping right’!
Would you pop the big question to the special person in your life via an…
Marketing automation is indispensable – you know why?
For most professional marketers, automation software is already an everyday tool or at least at…
Eliminate wasted ad spend and improve conversions with LeadsRx
Marketing attribution is a popular topic these days, especially in light of marketing teams being…
Combine the power of business process automation, turnkey managed services and IP protection for maximum profitability
BitTitan, a pioneer in Managed Services Automation, just expanded its MSPComplete platform with the addition…
LinkedIn Lead Gen Forms makes collecting quality leads easy
For many marketers, collecting quality leads is hard. On mobile, it’s even harder. That’s because…
eMarketer.com: Most marketers only use basic email automation
Almost two-thirds of email marketers worldwide use email automation, but more advanced automation techniques are…
Appointments & Announcements
Ogilvy & MatherFrancis Wee announced the appointment of one of the most…
Protect your brand by monitoring social media
Social media is a kind of love-hate relationship since it can like you, share with…
Livestreaming brings your campaigns to life
Livestreaming is a powerful emotionalizing medium for its users and many want to share their…
Social media overtakes print in ad spend
According to Zenith’s recently published Advertising Expenditure Forecast, social media ad spend is the fastest…
Website performance expectations are high in South East Asia – on all connected devices
Smartphones are the go-to device for accessing the Internet throughout South East Asia and consumers…
Alpha users
Just like viruses spread in nature, there is an initial starting point to communications in…